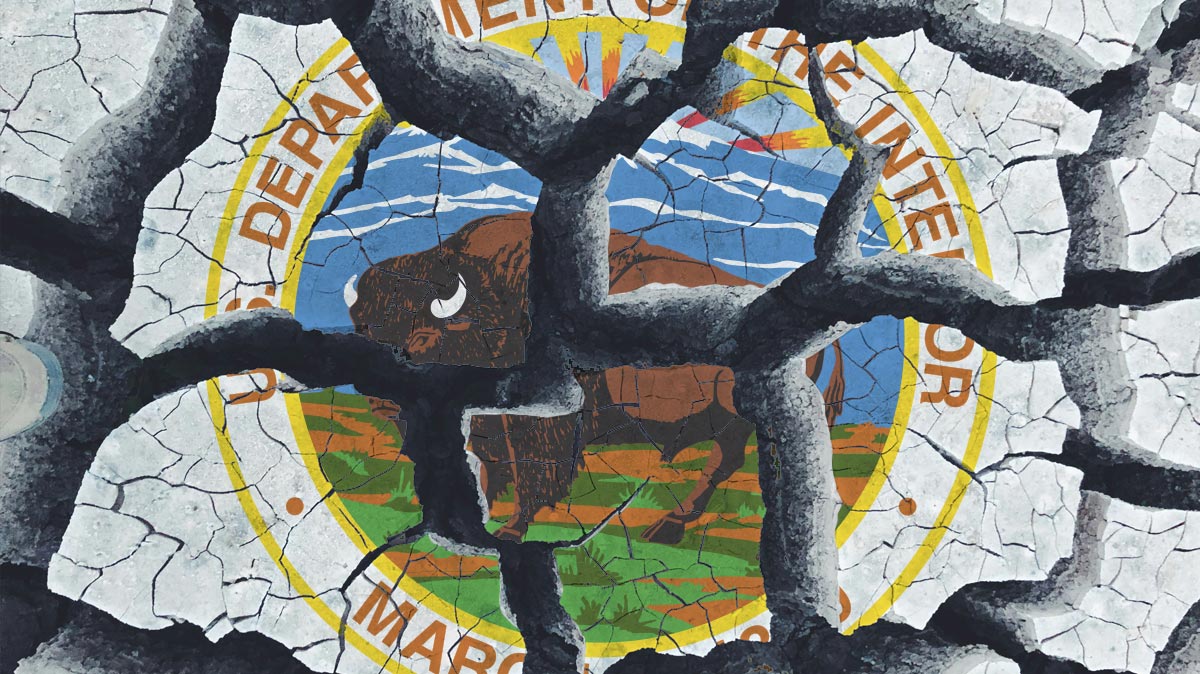
Passwords Cracked: The Security Gaps in the U.S. Department of the Interior's System
Baryo Bar Yosef
SEPTEMBER 6, 2023 • 1 MIN READ
Passwords are the frontlines of cybersecurity, but a recent inspection on the U.S. Department of the Interior paints a sobering picture of the true state of password security. As engineers, these findings should give us pause, urging us to reassess how we approach authentication systems in our projects.
A Worrying Scenario
Let's start with the alarming statistics. During the inspection, a staggering 21% of active user passwords were cracked. Of these, 288 were accounts with elevated privileges and 362 were accounts belonging to senior U.S. Government employees. Within the first 90 minutes of testing alone, 16% of the department's user accounts were compromised. Even so-called "strong" passwords like "Nationalparks2014!" fell to the scrutiny of the testing tools.
The Hashed Password Fallacy
A noteworthy point was raised regarding hashed passwords. Conventional wisdom dictates that hashed passwords are secure.



